Muucmf T6 CMS contains Reflected XSS in /channel/admin.Account/autoReply.html?keyword=
Muucmf T6 CMS contains Reflected XSS in /channel/admin.Account/autoReply.html?keyword=
1. Description:
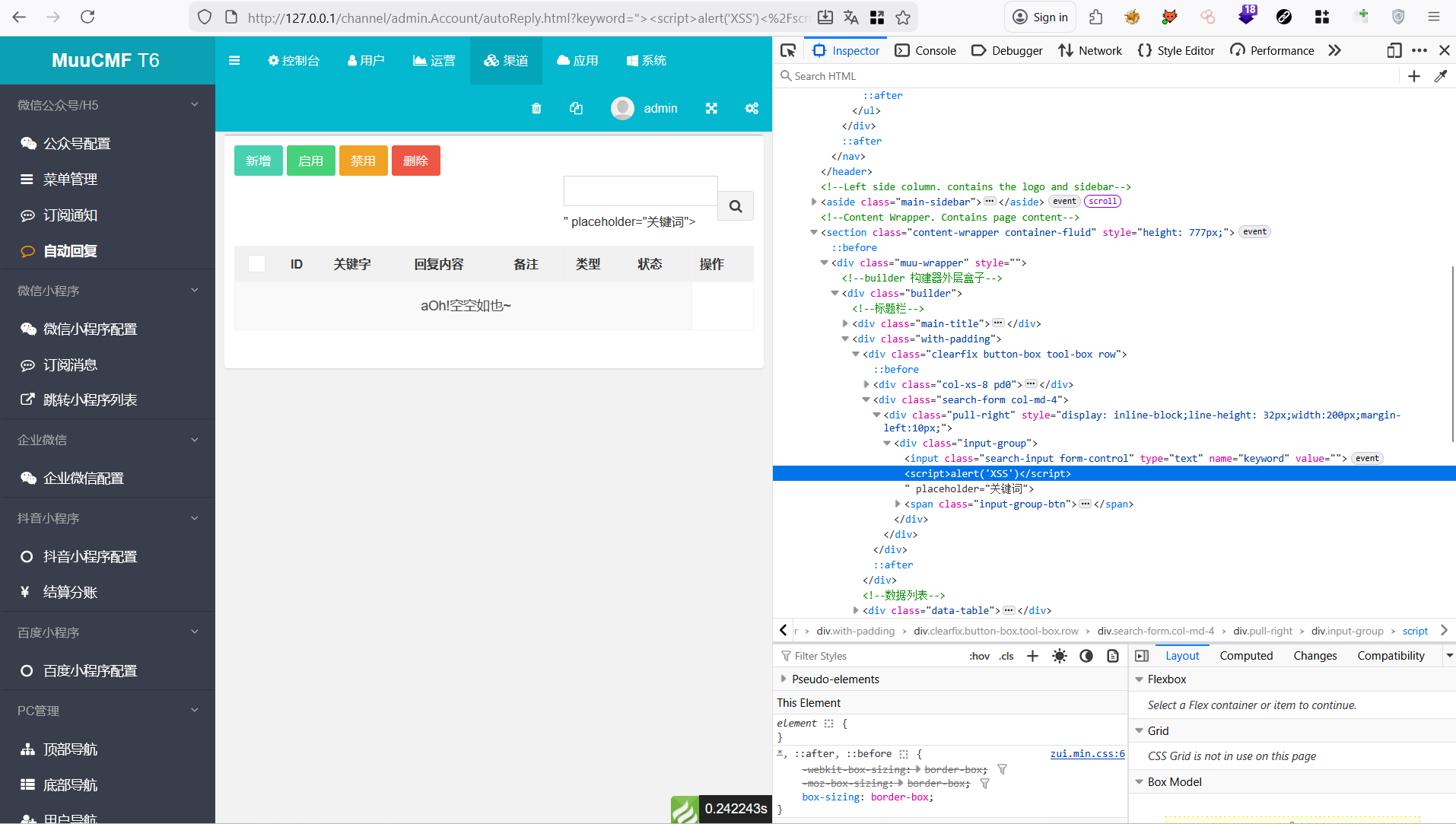
Reflected Cross-Site Scripting (XSS) in MuuCmf T6 v1.9.5.20260309 allows a remote attacker to execute arbitrary JavaScript code in the context of the user’s browser session via the keyword parameter to the channel/admin.Account/autoReply.html endpoint.
Vulnerability: Reflected XSS
CVSS score: 8.8 (High)
Vector String: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
2. Ananlysis
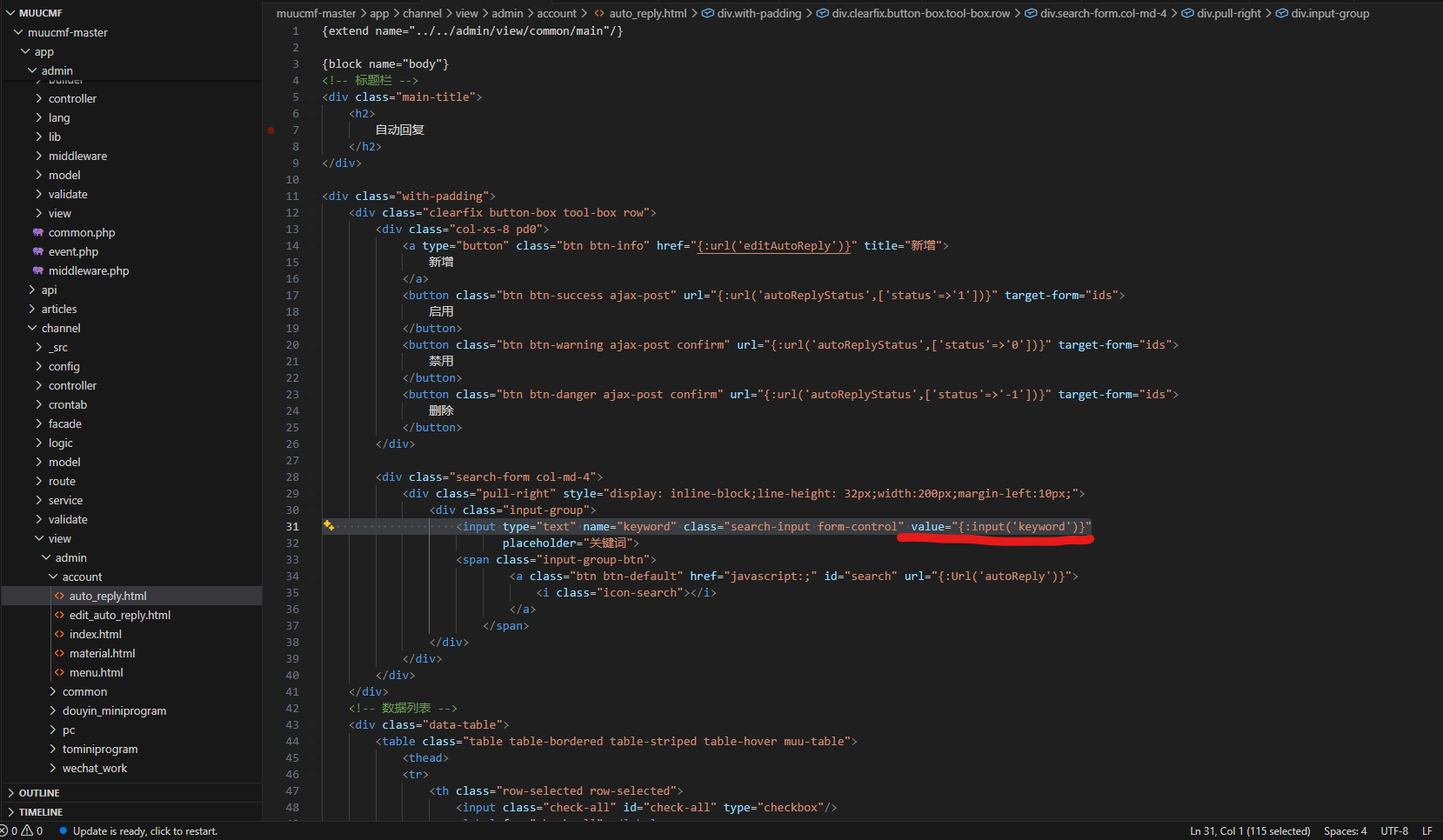
In the muucmf-master\app\channel\view\admin\account\auto_reply.html file, line 31 the value of input tag is using input from user without filter or santitize and the data is reflected in website leak to XSS vulnerability.
3. POC
Inject XSS payload to endpoint http://127.0.0.1/channel/admin.Account/autoReply.html?keyword= and the payload will execute.
Video demo:
This post is licensed under CC BY 4.0 by the author.